Infographics
Smart Home IoT
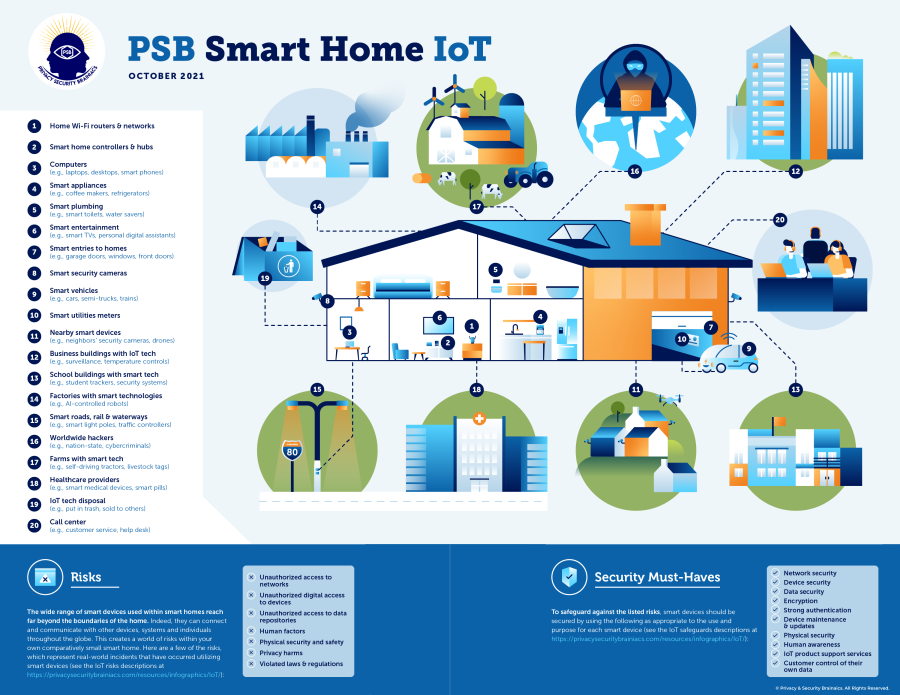
Each environment where IoT products are used needs to have risk mitigation controls implemented as appropriate to the associated digital ecosystem to most effectively mitigate the most cybersecurity and privacy risks. However, most consumers, and businesses with no IoT product cybersecurity or privacy experts on staff or contract, simply aren’t aware of how to determine these risks.
This infographic highlights many common types of these risks. View more information on the IoT Security and Privacy page.

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
6 Places Crooks Steal (Then Ransom) Your Data
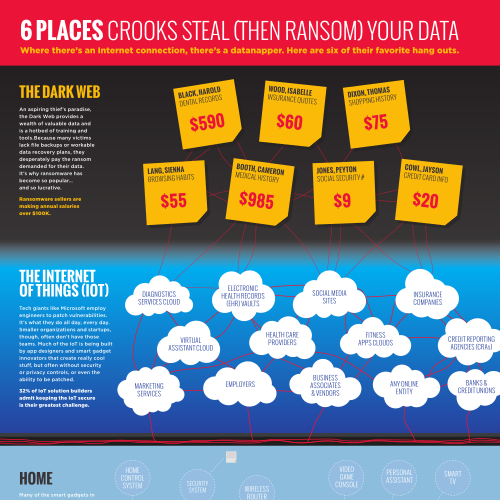
Where there's an Internet connection, there's a datanapper. Here are six of their favorite hangouts.

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
Your Health Data: Available For the Taking
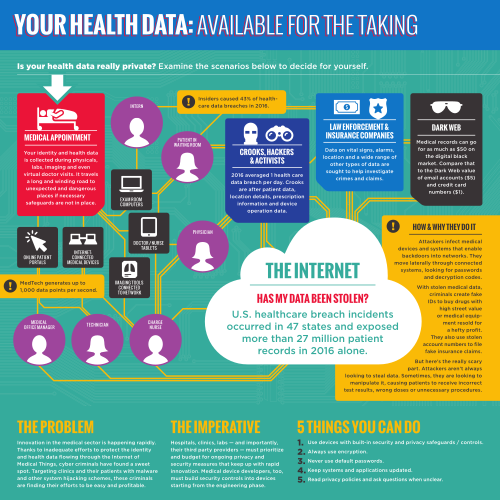
Is your health data really private? Examine these scenarios and decide for yourself.

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
Who Has Your Health Data?
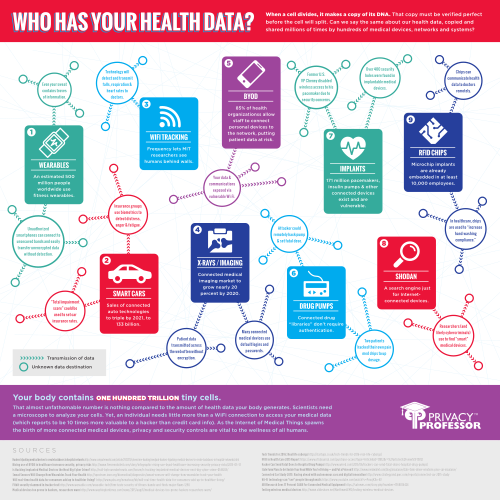
When a cell divides, it makes a copy of its DNA. That copy must be verified perfect before the cell will split. Can we say the same about our health data, copied and shared millions of times by hundreds of medical devices, networks and systems?

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
How Many Times a Day Are You Handing Over Your Information?
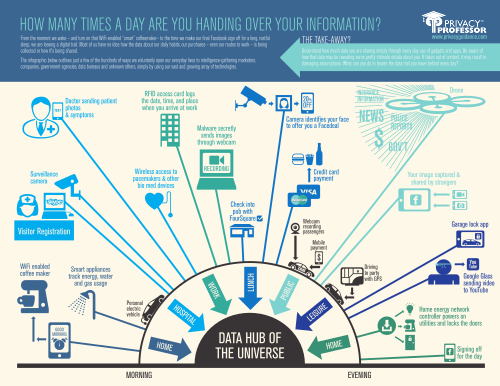
From the moment we wake – and turn on that WiFi-enabled “smart” coffeemaker– to the time we make our final Facebook sign off for a long, restful sleep, we are leaving a digital trail. Most of us have no idea how the data about our daily habits, our purchases – even our routes to work – is being collected or how it's being shared

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.